CodeOne
Sentinelle
Sentinelle (Security Operations Hyper-Automation Solution)
Codeone Co., Ltd.'s AI security control automation solution, Sentinelle, automatically processes security events in conjunction with SIEM solutions, suggests the best analysis plan, and detects hidden threats by inspecting simple logs. In addition, you can see the entire security situation at a glance and detect and analyze related threats to minimize cyber attack damage through quick response.
Sentinellef Features
Expected effects upon introduction verified by various control sites such as companies/institutions
Sentinelle Key Features
Automatic processing and management of security events
AI-enabled security threat inspection
AI suggested processing list
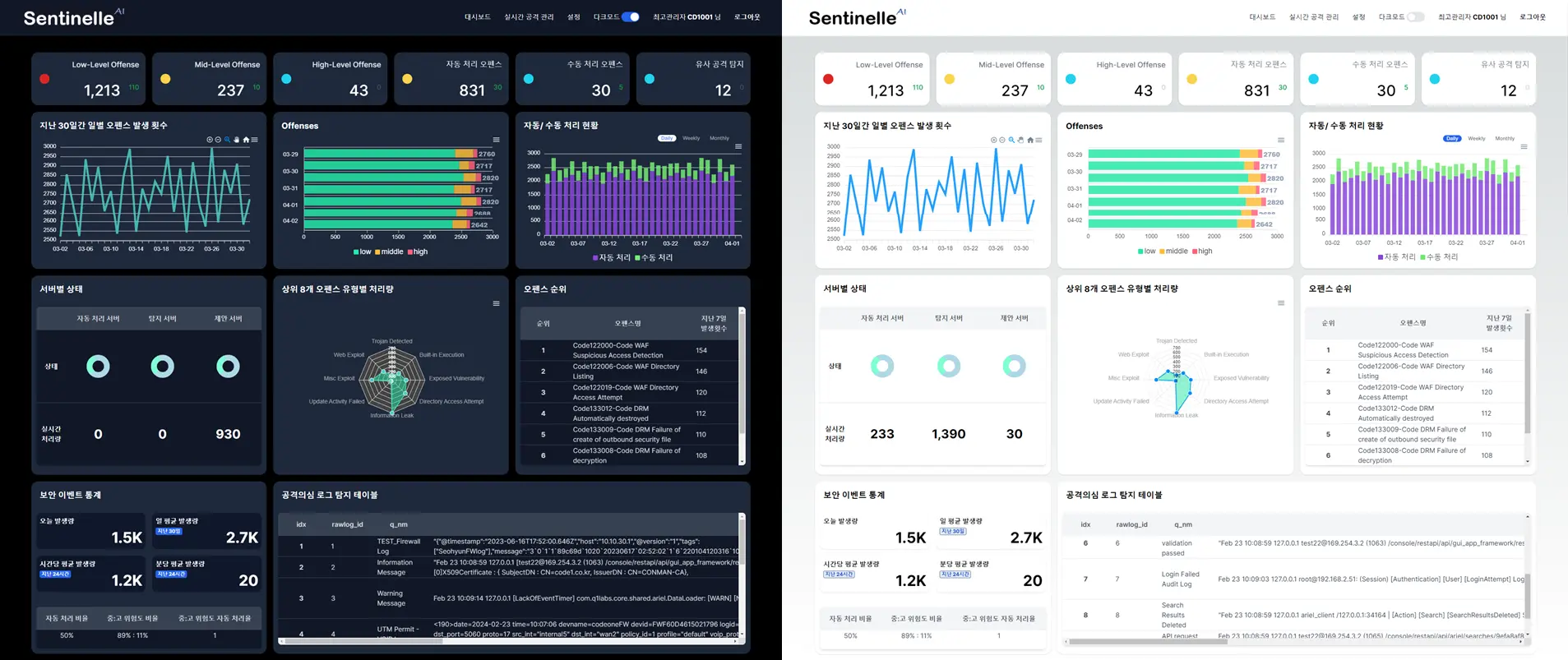
Security threat real-time dashboard
Expanded features: generative AI linkage, automatic report
cost savings
Areas requiring Sentinelle AI security control automation solution
Types of companies that need Sentinelle AI security control automation solution
Intellectual property rights and key adoption cases
6 domestic patent registrations, 1 Japanese patent application (domestic patents 10-2794551, 10-2749050, 10-2744019, 10-2744022, 10-2744024, 10-2806577, Japanese application 2024-145878)
2024 Ministry of Science and ICT, IITP SW R&D Awards Ceremony: Received the Director Award from the National Institute of Information and Communications Planning and Evaluation
Central Election Commission: Establishment of Sentinelle through security control center SIEM advancement project
Built in the control center of major public institutions Next-generation AI security control automation solution: Code One Sentinelle
Sentinelle is a security control automation platform based on artificial intelligence (AI). Achieve integrated threat management and intelligent response even in complex security infrastructure environments. We respond quickly and accurately to cyber attacks with processing strategies accumulated through verification in actual security control environments. Integrated management of security data through linkage with various security systems and SIEM solutions, effectively detects even covert attacks and unknown new attacks. The AI-based analysis engine goes beyond policy-based detection to identify potential attacks, automatically classifies and processes detected security events, or suggests prioritized optimal response plans depending on the situation, supporting quick and accurate decision-making by security personnel.
In addition, an explainable artificial intelligence (XAI) dashboard visually expresses detection grounds and risk factors, helping administrators clearly understand detection results and implement data-based responses. Sentinelle has excellent processing performance to reliably handle large-scale security events and scalability and flexibility to flexibly respond to changing security environments. In addition, it provides an integrated control dashboard that allows operators to check the entire process of occurrence - analysis - response at a glance, further enhancing the operator's security control experience. In addition, we provide consulting, training, and service support for products according to the needs of companies and organizations. We use our extensive construction experience to ensure smooth operation of products introduced by actual companies, and continuously provide updates and maintenance for products.
With Sentinelle, Security control becomes faster, more accurate and smarter
What is Sentinelle?
Sentinelle (Security Operations Hyper-Automation Solution)
Deployment Model
AX (AI Transformation)
Key Features
Security Operations Center Support Features
Why use Sentinelle?
The Need for AI Security Event Automatic Processing System
Product Introduction
Product Features
Auto-Processing
Solution-Suggestion
Similarity-Detection
Timeline-Management
Ticket-Management
Graphics
Reports
1. Threat Auto-Processing Function
AI automatic processing for low-level threats and designated specific attacks
· Ability to configure automatic processing for specific attacks
· Automatic processing of 20 million low-level attacks in 24 hours (based on 21 people working in 3 shifts for 24 hours, processing 10,000 per day/21 people)
· Verification of automatic processing results and statistics
· View of attack occurrence status by level
<Threat Auto-Processing Function>

