IBM
Qradar SIEM
What is Qradar SIEM?
IBM Security QRadar
A next-generation SIEM providing precise, comprehensive correlation analysis and compliance management
QRadar SIEM provides an integrated view of logs, event data, network flows and packets, vulnerabilities, asset data, and threat intelligence,
supporting distributed architecture and horizontal scaling for optimal implementation tailored to enterprise business scale.
Why QRadar?
The Need for QRadar SIEM
Product Introduction
Product Features
Intelligence
Gartner
Cases
1. Qradar's Security Intelligence
Product Introduction
Key Functions
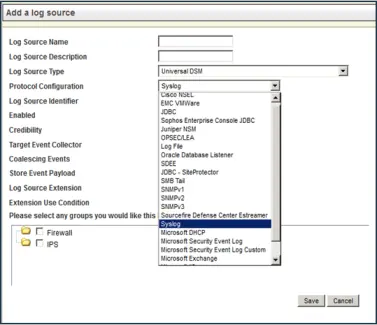
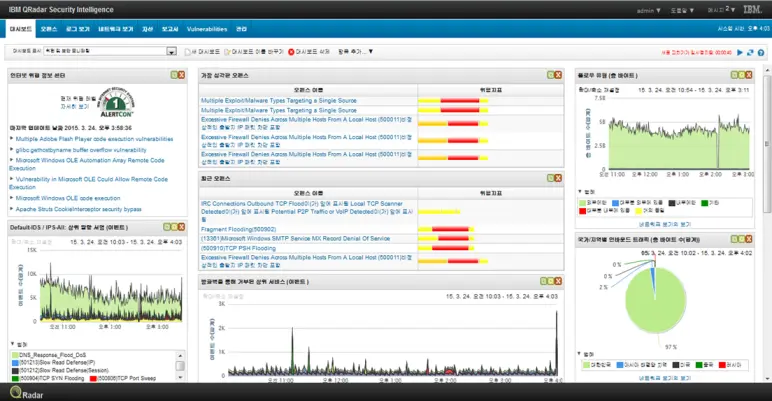
Log Collection and Normalization
Supports various protocols for log collection, and provides uDSM (Universal Data Source Module), a user-defined log format for collecting, analyzing, and searching unsupported logs.
For syslog format logs that are supported by default, the Auto-Discovery function is supported, which automatically parses the format and registers the data source when logs are transmitted without a separate registration process.
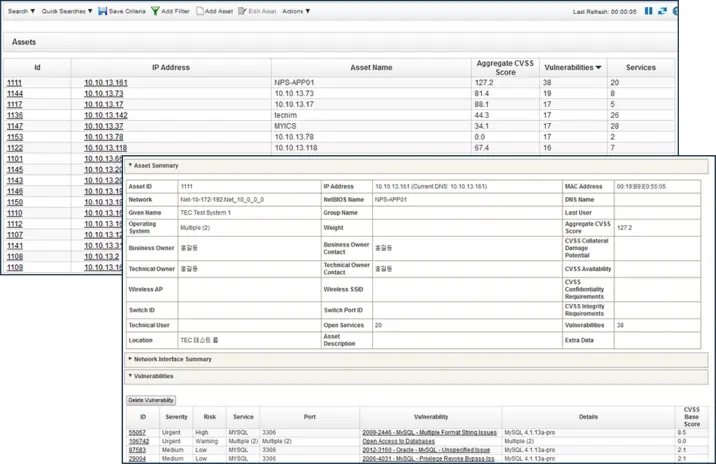
Asset Profiling
Profiles and manages asset information identified through logs, flows, vulnerability diagnostics, etc., using managed asset information for correlation analysis, event tracking, and vulnerability information profiling.
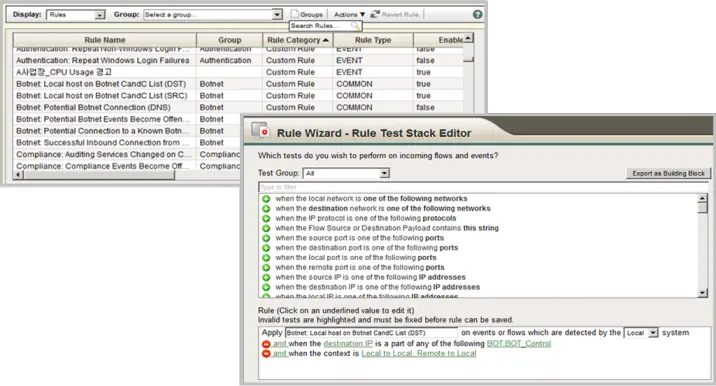
Comprehensive Correlation Analysis Rules
Provides comprehensive correlation analysis rules and rule sets that analyze and interpret collected information such as logs, flows, and vulnerability information in real-time from various aspects.
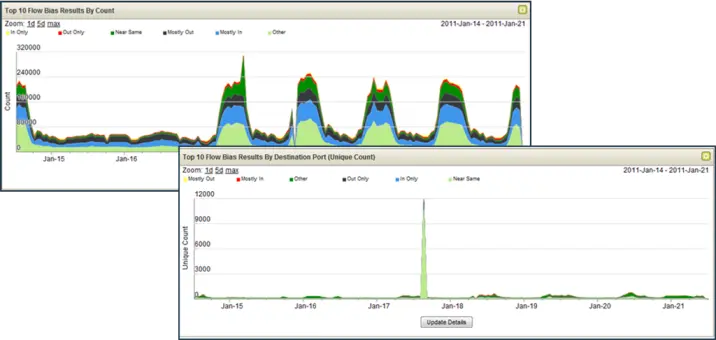
Anomaly Detection
In addition to correlation analysis, provides real-time Network Anomaly Behavior Detection (NBAD) functionality based on learned data.
Uses NBAD to respond to unknown attacks.
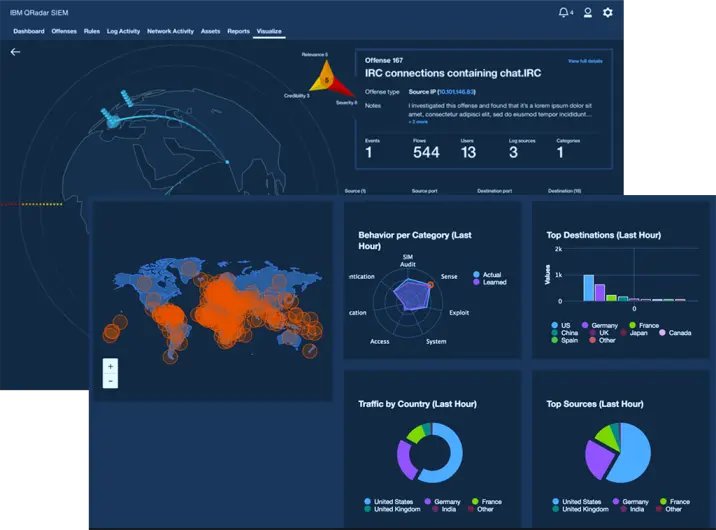
Centralized Web-Based UI/Dashboard
Provides a centralized web-based UI and dashboard.
Administrators/users connect to the UI using a browser to simultaneously perform monitoring and management activities.
Qradar Pulse Dashboard
Product Introduction
Expected Benefits
Improved Compliance

Faster Threat
Detection and Resolution
Reduced Internal Fraud,
Theft, and Data Leakage
Minimized Risk through
Exploit Prevention
Uptime

