Group-IB
ASM(Attack Surface Management)
What is ASM?
ASM(Attack Surface Management)
ASM is a solution that helps prepare for attacks by continuously detecting external IT assets exposed to the outside world and identifying vulnerabilities and threats.
It analyzes categories for the eight major threats and provides notifications about threats.
(Vulnerabilities, network security, leaked account information, malware activity, dark web mention confirmation, SSL/TLS security, email security, DNS/domain security)
Why ASM?
The need for external surface management
The External Attack Surface
Legacy solutions, creating information security blind spots by expanding processes and infrastructure

Necessity according to market and experts
Gartner announces key security and risk management trends for 2022
· Recent risk management trend: expansion of attack area
The attack surface of companies is expanding. Exposed by risks associated with the use of cyber-physical systems, IoT, open source code, cloud applications, complex digital supply chains, social media, and more, organizations have moved beyond their controllable set of assets. Organizations must manage a broader range of security exposures beyond traditional approaches to security monitoring, detection, and response. <emphasis>EASM (External Attack Surface Management) technology and CAASM (Cyber Asset Attack Surface Management) should help CISOs visualize internal and external business systems to automate the discovery of security coverage gaps.
IBM, Cost of a Data Breach Report 2023
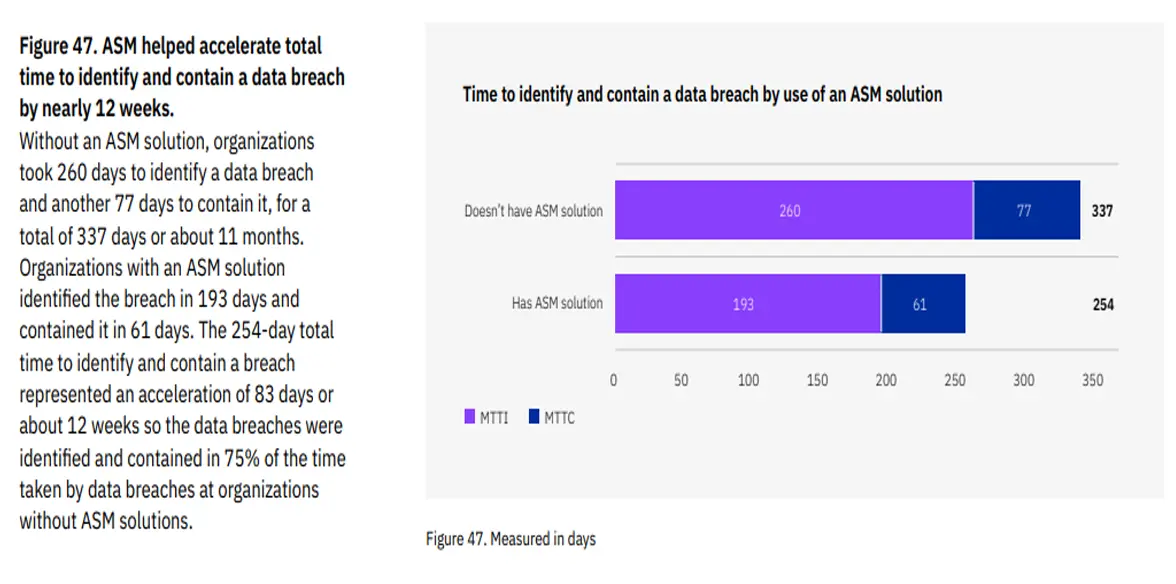
[Organizations that have an ASM solution save 25% of the time to recognize and respond to leaks compared to organizations that do not have an ASM solution.]
Product introduction
Main features
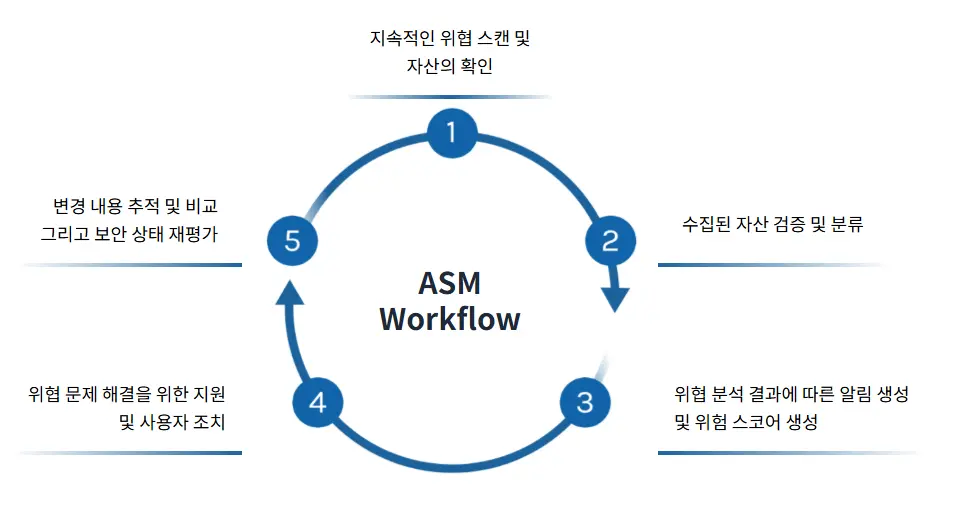
Group-IB ASM Workflow
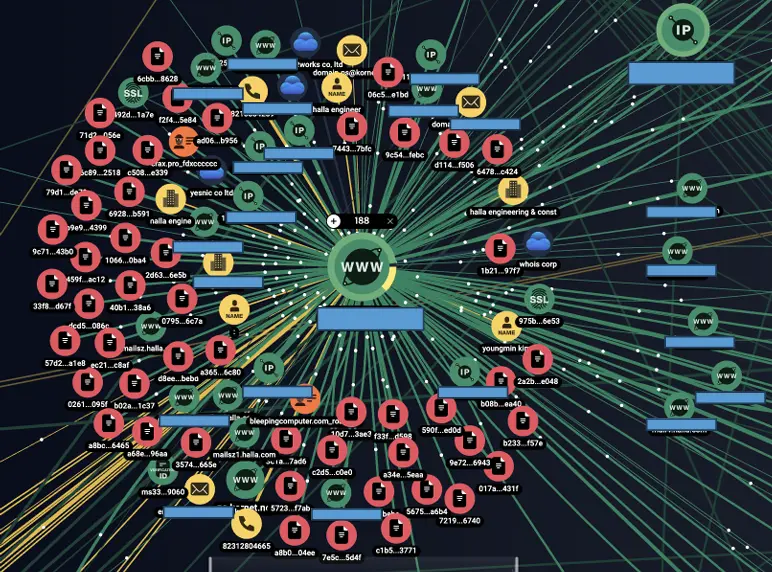
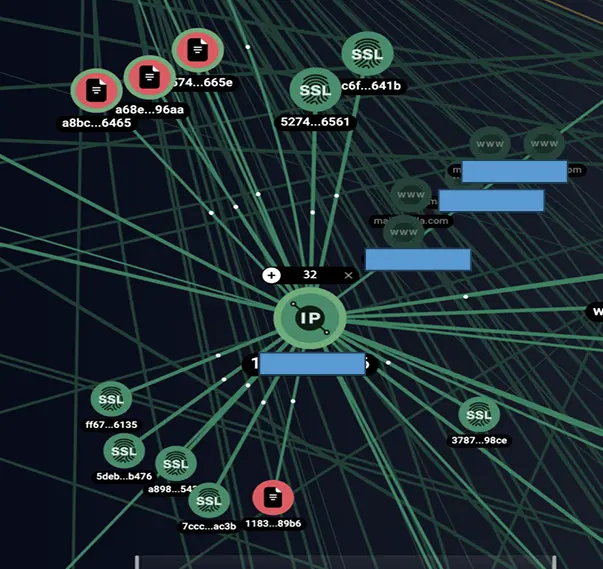
Group-IB ASM graph
Provides an integrated graph containing past change history using web snapshot technology (Includes information on malware, phishing, C2 servers, and threat actors, providing visibility into relationships between assets)